INTRODUCTION
UNDERSTAND THE MAIN CONCEPT
These programs also allow you to monitor network activity recording data (usernames, passwords; ect.) each time they access other computers on the network.
These programs aim at monitoring ("sniffing") network traffic to capture access to network services, such as remote mail service (IMAP, POP3), remote access (telnet, rlogin, etc.), file transfer (FTP) etc.. accesses made, capturing packets. Always aimed at getting the most relevant information.
When we called the HUB computer and send information from one computer to another, in reality this data is for all ports of the HUB, and therefore for all machines. It turns out that only the machine on which the information was intended to send the operating system.
If a sniffer were running on other computers, even without these systems sending data it travels there for the operating system, the sniffer will intercept at the network layer, capturing the data and displaying them to the user, in an unfriendly way. Generally the data is organized by type of protocol (TCP, UDP, FTP, ICMP, etc...) and each package read may have show your content.
YOUR PASSWORD CAN BE CAPTURED BY SNIFFERS!
To have access to these services, you first have to have a "log in". The login sequence - is part of the authentication protocol, which occurs at the beginning of each session - the "sniffers" are concerned about this, because it is this part that is your password. Therefore, it is only the filter "strings" keys that the password is obtained.
STEP BY STEP
Currently, almost all environments use switches and not hubs, which makes sniffing a little more difficult because the switches do not send the data to all ports as a hub does, it sends directly to the port where the host destination is. So if you try to sniff a network switch you will only hear what is broadcast, or its own connection. To be able to hear everything without being the gateway of the network, an ARP spoof attack (aka ARP poisoning) is necessary, or burst the CAM table of the switch.
Basic Usage
Now let's get our hands dirty: I'm assuming you already have the program (WireShark) installed, if you do not then download it. When starting WireShark, the displayed screen will look something like Figure 1:
Figure 1) Wireshark.
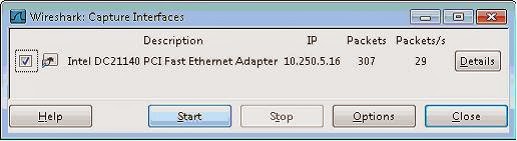
Before you can start capturing packets, we have to define which interface will "listen" to the traffic. Click Capture > Interfaces
Figure 2) Interfaces.
From there, a new window will appear with the list of automatically detected interfaces, simply select the desired interface by clicking the box next to the name of the interface, as in figure 3:
Figure 3) Capture Interfaces.
If you click Start, it will begin automatically capturing packets. You can select the interface and only then it will start the capture if necessary.
When the capture process starts, you will see several packets traversing the screen WireShark (varying according to the traffic of your machine / network). Will look something like the figure 4:
Figure 4) Capturing.
To stop the capture, simply click the button, "Stop the running live capture".
Figure 5) Stop.
It is important to remember that you must take care if your network is busy, the data stream may even lock your machine, then it is not advisable to leave the WireShark to capture for a long time, as we will see, we will leave it running only during the process to debug a connection. The greater the amount of packets, the longer it takes to apply a filter, find a package, etc.
With this we have the basics of the program, we can set the capture interface, start and stop the capture. The next step is to identify what interests among many packages. For this, we will start using filters.
Using Filters
There are a plethora of possible filters, but at this moment we will see just how to filter by IP address, port and protocol.
The filters can be constructed by clicking on "Filter", then selecting the desired filter (there is a short list of pre-defined filters), or by typing directly into the text box. After you create your filter, just click "Apply", if you wanted to see the entire list of packages again just click "Clear", this will remove the filter previously applied.
Figure 6) Filter.
I will use a small filter list as an example:
Figure 7) Example by Rafael Souza (RHA Infosec).
It is also possible to group the filters, for example:
ip.src == 10.10.10.1 && tcp.dstport==80 OR ip.src == 10.10.10.1 and tcp.dstport==80
Source address 10.10.10.1
And destination port 80
CAPTURING PASSWORDS
Now we will see how you can capture passwords easily, just by listening to traffic. For this example we will use the POP3 protocol, which sends the data in clear text over the network. To do this, start capturing packets normally and start a session with your POP3 email server. If you use a safer protocol like IMPAPS or POP3 and I just wanted to see the functioning of the mechanism, it is possible to connect via telnet to POP3 without having to add / modify your account, simply run the following:
telnet serveremail.com 110
user user@rhainfosec.com
pass rhainfosecpasswd
Now stop the capture, filter and put "pop" and then click "Apply". now thats done, you see only the packets of POP3 connection. Now click on any of them right, and then click "Follow TCP Stream".
Figure POP3.
With this we will open a new window with the entire contents of the ASCII connection. As the POP3 protocol sends everything in plain text, you can see all the commands executed, including the password.
Figure 9) Pass.
This can be transported to any connection in plain text, such as FTP, Telnet, HTTP, etc.. Just to let you change the filter and examine the contents of the connection.
Importing External Captures
Usually in servers, there is no graphical environment installed and with that you cannot use WireShark directly. If you want to analyze traffic on this server and you cannot install WireShark, so you have to capture this traffic elsewhere, the best one can do is write traffic with TCPdump locally and then copy this dump to a machine with WireShark from where a more detailed analysis is made.
We will capture everything that comes and goes from the host 10.10.10.1 with destination port 80 and save content in capturerafaelsouzarhainfosec.pcap file from the local folder where the command was executed. Run the server:
tcpdump -i eth0 host 10.10.10.1 and dst
port 80 -w
capturerafaelsouzarhainfosec.pcap
Once you're finished capturing, simply use CTRL + C to copy the file to the machine WireShark capture and import by clicking on File -> Import. Once imported, you can use the program normally as if the capture had occurred locally.
EVOLUTION OF THINKING
Why steal your password?
There are various reasons that lead people to steal passwords from simply to annoy someone (sending email as you) up to perform illegal activities (invasion on other computers, theft of information, etc.) An attraction to crackers is the ability to use the identity of others in these activities.
One of the main reasons that attackers try to break systems and install "sniffers" is the ability to quickly capture the maximum number accounts. Thus, the more accounts this attacker has , the easier it is to hide your stash.
How can you protect yourself?
Do not think that "sniffers" can make all the whole internet insecure. It is not so. You need to be aware of where the risk is , when you're at risk and what to do to be safe .
When you have your credit card stolen or suspect that someone may be using it improperly, you cancel the card. Likewise, as passwords can be stolen, it's critical that you replace it regularly. This precaution limites the amount of time that a stolen password can be used by an attacker.
Never share your password with others. This sharing makes it difficult to know where your password is being used (exposed) and is harder to detect unauthorized use. A password is like a tooth brush never share it and change it regularly.
Never give your password to anyone that is claiming they need access to fix your account problem or wanting to investigate the breach of a system. This trick is one of the most effective methods of hacking, known as "social engineering."
Use networks you can trust
Another aspect you should take into consideration is what network you can trust and which you cannot. If you are traveling and need to access an organizations computer remotely have a great level of assurance that the network is secure. For example, pick any file in your home directory that you share is it available to a "LanHouse" or network of another organization . Are you sure you can trust the network?
If you have no alternative for secure remote access and only have available resources such as telnet, for example, you can "mitigate" this effect by changing the password at the end of each session. Remember that only the first packet (200-300 bytes)of each session carry information from your "login". Therefore, to always change your password before logging out, this will not be captured and password before it that were exposed to the network are no longer valid. Of course it is possible to capture everything going across the network, but the attacker has no intention of filling their file system quickly and becoming so easily discovered.
Why are networks so vulnerable to "sniffers"?
There are several reasons and there is no quick solution to the problem.
Part of the problem is that companies tend to invest in more new features rather than add security. New security features can create the most difficult systems to configure and less convenient to use. Remember companies try to adhere to the C.I.A. triangle (confidentiality, integrity, and availability). New features create unintended effects on availability when this happens policy is overlooked creating a new vulnerability in itself.
Another part of the problem is related to added costs for Ethernet switches, hubs, network interfaces that do not support the particular "promiscuous" that sniffers can use.
CONCLUSION
The question that remains is how can we protect ourselves from this threat...
i) Network cards that cannot be put into "promiscuous" mode. Thus, computers cannot be mastered and transformed into "sniffers".
ii) Typically, the Ethernet interface only passes packets to the highest level protocol that are intended for local machine. Switching this interface into promiscuous mode allows all packets that are accepted and passed to the higher layer of the protocol stack. This allows the selection you want.
iii) Packages that encrypt data in transit over the network, thus avoiding to flow passwords "in the clear".
I would remind you that the safest thing to adopt and encourage the use of is software which enables remote access encrypted sessions, they help to make your environment much more secure.
One fairly common encryption technology currently in secure communication between remote machines SSH (Secure Shell). SSH is available for different platforms. Its use does not prevent the password captured, but as this is not an encrypted service to the attacker. SSH negotiates connections using RSA algorithm. Once the service is authenticated, all subsequent traffic is encrypted using IDEA technology. This type of encryption is very strong.
In the future, security will be increasingly intrinsic to the systems and infrastructure networks. No use having all the "apparatus" of security if you need, but do not use them. Security is not something that can be completely secure. Remember, no one is 100% secure.
Thank you readers, it's always good to help my dear friend Rafay Baloch















![SQL Injection Basics - Union Based [Detailed Tutorial]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjjQpa2wuMB-m5CXPVf71GUOkfiIOQA8KTyQ-_zfAl0SZa23UBN1QJaO2ZMGRDZlmDJTYf2jJ4ik3Xnj1locc38Yv9l6VMxTWt32s86JtXtLABDn20DRuAcbLPKMb9m2hc6PDmjIjvU-us/s72-c/SQL-Injection-Attack.jpg)




No comments:
Post a Comment